
How to Keep Your Business Safe from Growing Ransomware Threats
Ransomware attacks surged 75% in 2023. Learn how to protect your business from this growing threat with proactive security measures, employee training, and robust backup strategies.

24/7 monitoring and rapid response from Minnesota's assessment authority.
Best practices mean defense in layers. One breach can cost more than years of protection.
Proactive cybersecurity protects your operations, meets cyber insurance requirements, and prevents costly downtime that puts Minnesota businesses out of operation.
No single solution stops all threats. We implement multiple security layers—firewalls, endpoint protection, monitoring, and training—so if one fails, others still protect you.
Ransomware shutdowns cost $5,000-$50,000 per day in lost revenue. Our 24/7 monitoring and rapid response keeps your business running when others go dark.
Small businesses face the same threats as Fortune 500 companies. We right-size enterprise-grade security to fit growing Minnesota businesses' budgets.
From 24/7 threat monitoring to incident response and security training, we provide layered defense to protect your business from cyber threats.
24/7 threat monitoring and rapid response to security incidents
Enterprise-grade security operations without the enterprise cost
Identify and fix security weaknesses before attackers do
Under pressure, you don't rise to the occasion—you fall to the level of your training. Prepare your team to respond effectively before a real incident occurs.
Turn your employees into your best defense against cyber threats
Secure access for your remote and hybrid workforce, no matter where they work
A proven three-step approach to implementing and maintaining robust cybersecurity for your business.
We begin with a thorough cybersecurity assessment to understand your needs.
Our team implements tailored cybersecurity solutions to protect your business.
Enjoy continuous 24/7 IT support to maintain security and address any issues promptly.
We're not just another MSP offering basic security. We've secured Minnesota companies and institutions for 25 years—from Fortune 500 to 5-person businesses.
Every IT decision considers security implications. We don't just fix problems - we fix them securely, protecting your business from cyber threats.
Real security analysts monitoring your systems around the clock - not just automated alerts. Human expertise when you need it most.
You get the same level of service and attention we provide to our defense contractor clients - without the enterprise price tag.
We don't wait for alerts - our team actively hunts for threats in your environment before they become incidents.

Traditional antivirus is reactive - it blocks known threats after they're discovered. MDR (Managed Detection & Response) is proactive - it uses behavioral analysis, threat intelligence, and human expertise to detect and respond to threats in real-time, including zero-day attacks and advanced persistent threats that bypass antivirus.
Most SMBs (10-200 employees) can't justify the $500K+ annual cost of building their own SOC. Our shared SOC model gives you enterprise-grade security monitoring and incident response at a fraction of the cost - typically $2,000-$8,000/month depending on your environment size and complexity. Contact us at 651-448-9900 for a custom quote.
We recommend monthly penetration testing as a minimum (especially if we are not managing your desktops), with quarterly vulnerability scans. If you handle sensitive data (HIPAA, PCI-DSS, CMMC), have experienced recent breaches, or are making significant infrastructure changes, more frequent testing is advised. Why? Because humans make mistakes—it's inevitable. Our testing catches those mistakes before attackers exploit them.
More than likely, we're going to know before you do. Attackers don't strike right away—they 'wait it out,' spending weeks quietly learning your environment to extract maximum damage. Our 24/7 monitoring catches them during this reconnaissance phase, before they can strike. Once we detect an attack, we execute our Incident Response Procedure immediately: containment, investigation, eradication, and recovery—with support from law enforcement and insurance if needed.
Yes. We specialize in compliance-driven security. Our team has deep expertise with NIST 800-171, HIPAA, PCI-DSS, SOC 2, and CMMC. We'll design your security architecture to meet compliance requirements while maintaining usability for your team. For defense contractors, check out our free CMMC ROI Calculator and CMMC CFO Planner tools to understand compliance costs and timelines.
C3PAO-authorized assessments and full NIST 800-171 implementation for defense contractors pursuing CMMC certification.
Meet underwriting requirements, implement required security controls, and reduce premiums with proven cybersecurity practices.
Executive-level security strategy and leadership without the full-time cost - perfect for organizations without dedicated security teams.

Ransomware attacks surged 75% in 2023. Learn how to protect your business from this growing threat with proactive security measures, employee training, and robust backup strategies.

Discover how partnering with a managed security service provider (MSSP) can enhance your security posture, fill IT gaps, and reduce costs while providing 24/7 protection.

Essential strategies and best practices to protect your business from ransomware attacks and recover quickly if compromised.
Download Free
Learn why multi-factor authentication is essential for business security and how to implement it across your organization to prevent account takeovers.
Download Free
Understand and mitigate insider threats with strategies to protect your business from malicious employees, contractors, and accidental data breaches.
Download Free
A comprehensive checklist to help protect your organization's sensitive data and maintain robust privacy practices.
Download Free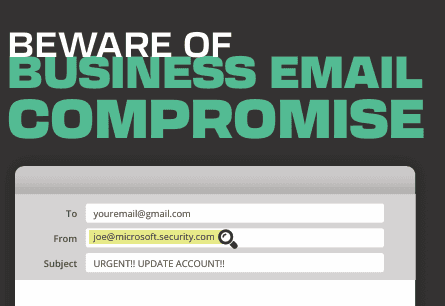
Learn how to identify and prevent business email compromise attacks that target your organization's financial transactions and sensitive communications.
Download Free
Essential facts and statistics about encryption technology and its critical role in protecting your organization's sensitive data.
Download FreeSchedule a free security assessment to identify vulnerabilities and get a customized protection roadmap.